Storing Daily call recordings in a custom Amazon S3 bucket
Developers can configure Daily to store call recordings in an Amazon S3 bucket of their choice. In this configuration, Daily does not store the recording on its own servers at any point in the process; recordings are written directly into the specified bucket.
In this guide, we'll go through how to configure S3 storage for Daily call recordings. Specifically, we will cover the following steps:
- S3 bucket configuration requirements
- Creating an IAM policy with appropriate permissions
- Creating an IAM role for Daily to assume for storage
- Configuring your Daily domain or room to store recordings in S3
If you're new to call recording with Daily, check out our guide about recording calls with the Daily API
S3 bucket configuration requirements
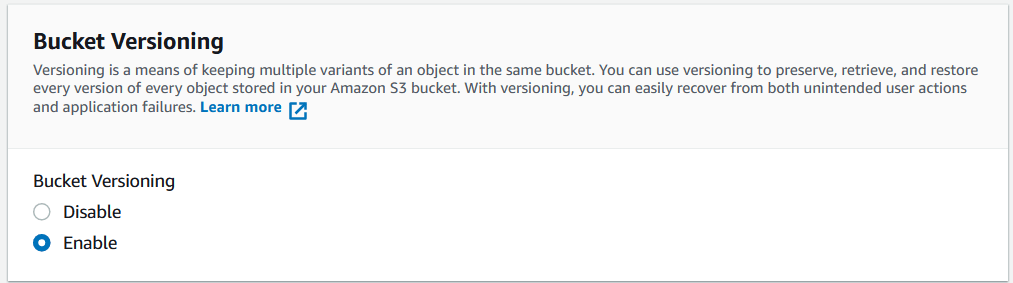
The target S3 bucket to which you want recordings to be stored can be in any AWS region and must have versioning enabled. Please be sure to select "Enable" under "Bucket Versioning" when creating your S3 bucket for recording storage.
Shortcut: A custom Daily script to get set up
To help developers move faster, our team has created a GitHub repo with a custom script that will configure your S3 bucket for Daily recordings.
To use this script, you will need:
- A Daily domain name. Create a Daily account if you haven't already. Your Daily domain name is the subdomain of your Daily room links. (E.g. If the room link is
https://devrel.daily.co/rec-guide,'devrel'is the Daily domain you would use here.) - The bucket name.
- The bucket region.
Follow the instructions in the README for more information.
Once you have run this script, you can jump to the end of this guide to configure your Daily rooms.
If you prefer to set the bucket up manually, keep reading.
Creating an IAM policy with appropriate permissions
AWS Identity and Access Management (IAM) is used to control access to various AWS resources, including S3 buckets. To allow Daily to store WebRTC call recordings into your designated bucket, Daily's account needs sufficient access to your bucket.
The first step to provide this access is to define an IAM policy with the appropriate permissions. The policy should be defined as follows:
Replace your-bucket-name in the "Resource" property above with the name of your designated S3 bucket.
To create the above policy, log into AWS and navigate to to the IAM dashboard. Click on "Policies" in the left hand menu. Next, click "Create" to paste the above policy into the JSON definition:
Creating an IAM role for Daily to assume for storage
The next step is to create an IAM role which will have the policy we created above attached to it. If you are already familiar with creating IAM roles, feel free to use the following values to create your role. If you'd like a bit more guidance on the process, you'll find it under the following role specification information.
IAM role specification for Daily call recording storage
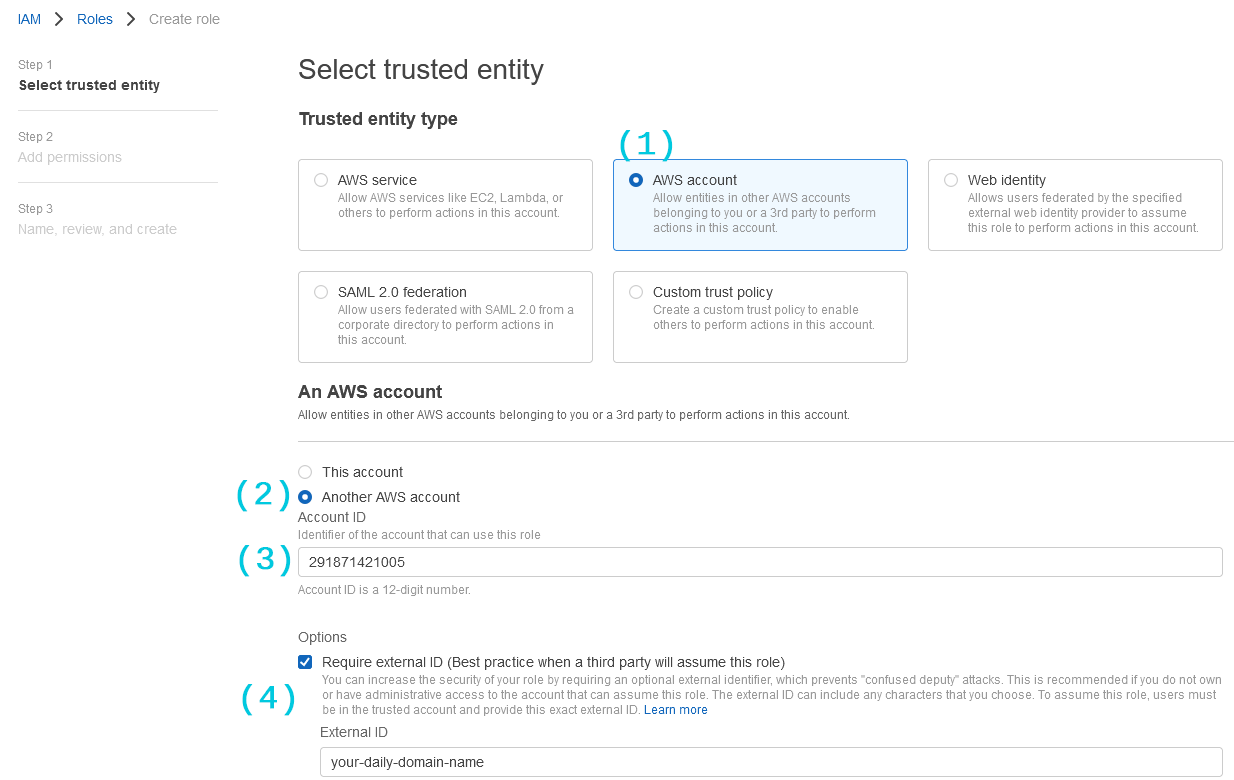
- Trusted Entity Type: AWS Account
- Trusted AWS account ID:
291871421005 - Required external ID: your daily domain name
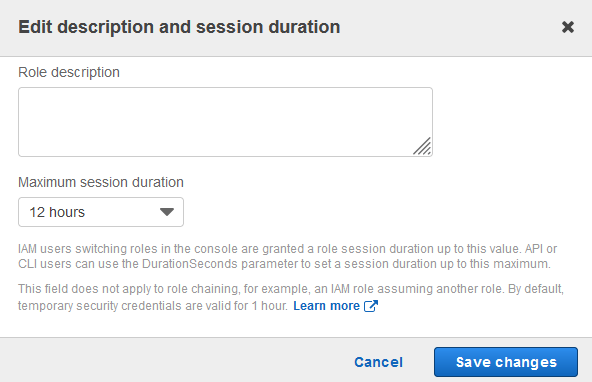
- Maximum session duration: 12 hours
IAM role creation walkthrough
You can find role creation in the same IAM service dashboard which we used to create the policy. Click on "Roles" in the left hand menu, then click "Create Role". Once on the role creation page, take the following steps to create your role:
- For "Trusted Entity Type", select "AWS Account"
- Under "An AWS Account", select "Another AWS account"
- Enter
291871421005as the Account ID (this is Daily's account) - Use your Daily domain name as the "Require External ID". Your Daily domain name is the subdomain of your Daily room links. (E.g. If the room link is
https://devrel.daily.co/rec-guide,'devrel'is the Daily domain you would use here.)
More on Daily domains
Your domain name can be found in the first part of any of your room URLs: https://[domain-name].daily.co/[room-name].
Use the value of [domain-name] as the required external ID in your AWS role configuration.
You can also find your domain name by going to the Daily dashboard. You will see your domain
as a query parameter in the URL once there: https://dashboard.daily.co/?domain=[domain-name].
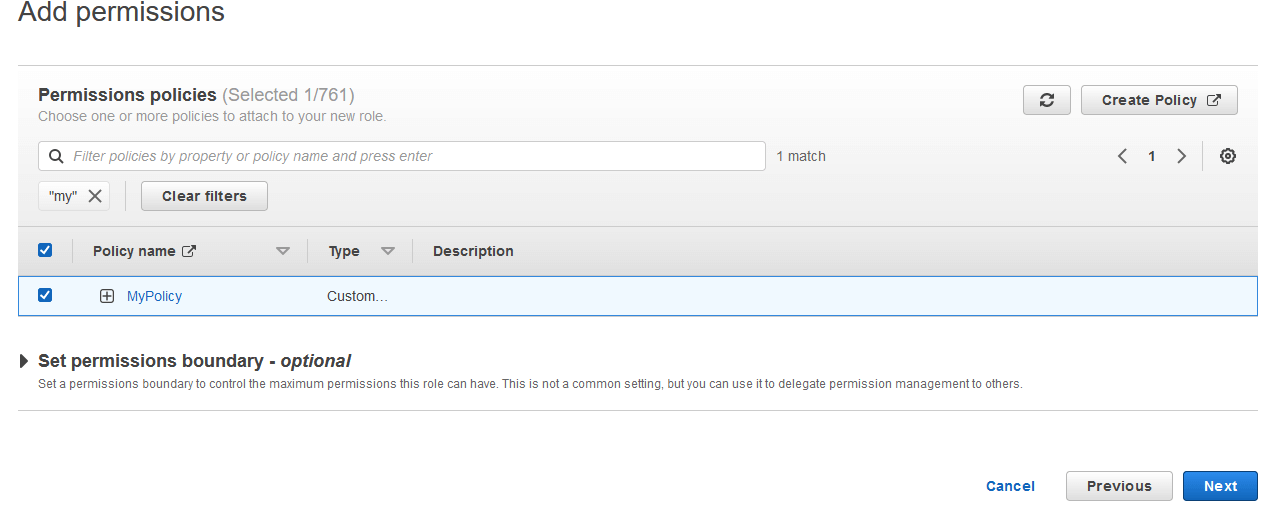
Click "Next" and attach the policy you just created to the role:
Click "Next" once more, give your role a name in the subsequent prompt, and click "Create role".
Once the role is created, find it in your IAM Roles list and click "Edit". Set the "Maximum session duration" to "12 hours":
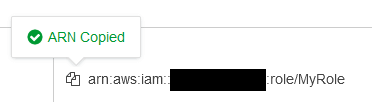
Finally, copy the ARN (Amazon Resource Name) of the role you just created on the role page in IAM:
With the policy and role in place, we are done with the AWS configuration.
Configuring your Daily domain or room to store recordings in S3
S3 storage can be configured at the room or domain level. The order of priority for call recording storage is as follows, in descending order:
- Customer S3 bucket configuration at the room level. You can configure a room with a custom S3 bucket via a POST request to the room endpoint. Alternatively, you can specify a recording bucket on room creation.
- Customer S3 bucket configuration at the domain level. This can be configured via a domain configuration POST request.
- Daily's own default bucket. This requires no configuration on the user's end.
Recordings stored in a customer's own S3 bucket do not incur an additional storage rate.
This API call uploads a test file with name daily-co-test-upload.txt to verify the permissions.
Examples
Here's an example of an API call to set a custom S3 bucket at the room level:
Here is an example of an API call to set a custom S3 bucket at the domain level:
To set recording behavior back to the default of using Daily's own storage, you can make a request to the above endpoints with "recording_bucket" set to null:
The properties specified in the config call are as follows:
bucket_nameis the name of your S3 bucketbucket_regionis the region in which you created your S3 bucketassume_role_arnis the ID of the role you created aboveallow_api_accessdictates whether Daily's recording access link API should allow downloading the new recording or not
Conclusion
We hope this guide was helpful in showing you how to store your Daily video call recordings in your own S3 bucket. If you have any questions or run into any issues with the setup, please contact us.